Die Zukunft des Gartens: Innovationen und Tre...
Autor Mär 16, 2026 0 10
Die Zukunft des Gartens: Innovationen und Tre...
Autor Mär 16, 2026 0 10
Kreative Aufbewahrungslösungen für kleine Räume
Autor Mär 10, 2025 0 21
Wie man ein beruhigendes Badezimmer in eine W...
Autor Feb 17, 2025 0 28
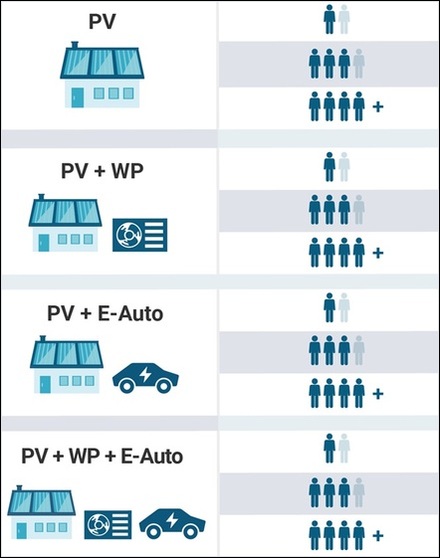
Bessere Chancen für Bauträger – trotz Krise z...
Autor Feb 12, 2025 0 24
[NEU] [hoch] MISP und MISP Modules: Mehrere S...
Autor Mai 15, 2026 0 1
[NEU] [mittel] vim: Mehrere Schwachstellen er...
Autor Mai 15, 2026 0 1
[NEU] [hoch] HCL BigFix: Schwachstelle ermögl...
Autor Mai 15, 2026 0 1
[NEU] [hoch] Red Hat OpenShift: Schwachstelle...
Autor Mai 15, 2026 0 1