Die Zukunft des Gartens: Innovationen und Tre...
Autor Mär 16, 2026 0 8
Die Zukunft des Gartens: Innovationen und Tre...
Autor Mär 16, 2026 0 8
Kreative Aufbewahrungslösungen für kleine Räume
Autor Mär 10, 2025 0 19
Wie man ein beruhigendes Badezimmer in eine W...
Autor Feb 17, 2025 0 18
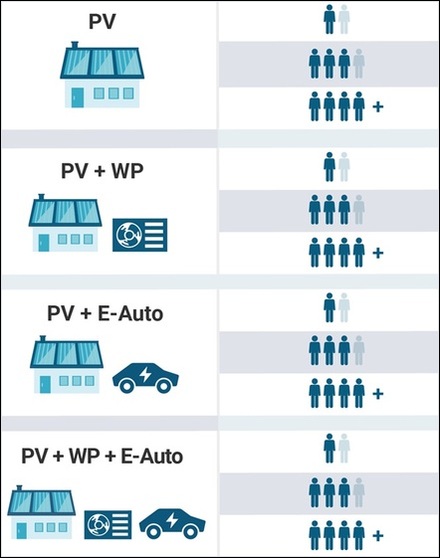
Bessere Chancen für Bauträger – trotz Krise z...
Autor Feb 12, 2025 0 22
[NEU] [mittel] Red Hat Hardened Images RPMs (...
Autor Apr 24, 2026 0 1
[NEU] [hoch] Tenable Security Nessus: Schwach...
Autor Apr 24, 2026 0 2
[NEU] [hoch] Microsoft Cloud-Produkte: Mehrer...
Autor Apr 24, 2026 0 1
[NEU] [hoch] Apache ActiveMQ: Mehrere Schwach...
Autor Apr 24, 2026 0 2